USA Accused For Planting "Flame" Malware to Hack France President's Network
A well known French newspaper named "L'Express" has accused that United States is using dangerous cyber weapon "Flame" to break into the computer networks inside France’s presidential palace also known as the Elysee. In his report L'Express has published details of what it claims was a sophisticated state-sponsored hack into the offices of the French presidency earlier this year with the intention of stealing data. According to the newspaper, the malware attack took place in May 2012, shortly before the second round of presidential elections in France, but has been kept secret until now. The newspaper alleges that the attackers reportedly found their targets on Facebook, identifying people working inside the presidential palace and connecting with them on the social network. The social engineering laid the groundwork for the next phase of the attack; the victims were then sent links to a fake Elysee intranet page where their login credentials were stolen. Workers at the Élysée Palace are said to have been befriended on Facebook by hackers, who then sent their victims a link to what purported to be a login page for the Élysée intranet site. In this way, it's claimed, login credentials were stolen. It is alleged that malware was then installed on the network, infecting computers belonging to senior political advisors, including Xavier Musca, Secretary-General of Nicolas Sarkozy's office. The United States Embassy in Paris has denied any involvement in hacking its ally. “We categorically refute allegations of unidentified sources,” Mitchell Moss, Embassy spokesman, told l’Express. “France is one of our best allies. Our cooperation is remarkable in the areas of intelligence, law enforcement and cyber defense. It has never been so good and remains essential to achieve our common fight against extremist threat.” Though the secretary of Department of Homeland Security Janet Napolitano did not deny the U.S. was involved. She told l’Express: “We have no greater partner than France, we have no greater ally than France. We cooperate in many security-related areas. I am here to further reinforce those ties and create new ones.”
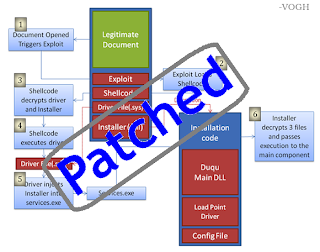
While talking about Flame, we would like to remind you that after the episode of 'Duqu'; In the middle of this year The Iranian Computer Emergency Response Team (MAHER) claims to have discovered a new targeted Stuxnet attacking the country's internal system. This newly found Stuxnet have been dubbed Flame (also known as Flamer or Skywiper). Flame the next generation cyber weapon which is also known as 'The Super Spy' has already fascinated the cyber-security industry with its sophistication and versatility as a Swiss-Army knife of cyber-spying. Later it was spotted in the wild when software giant Microsoft confirmed that its Windows Server Update Services (WSUS), Windows Update (WU) has been infected by Flame malware. Also in many fields, the name of 'Flame' was on the high node.
-Source (NS & threatpost)