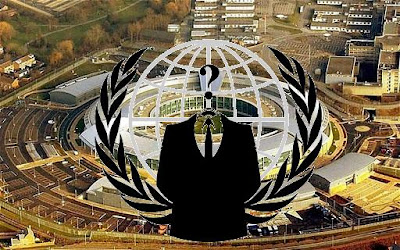
Anonymous Engaged Massive Cyber Attack To Bring Down British Prime Minister’s Office, Home Office & Ministry of Justice
One of the official twitter account of hacker collective Anonymous warned that they will engage cyber attack against the Govt of UK on 4th of April. The tweet said:- "EXPECT a DDOS (Distributed Denial of Service) every Saturday on the UK Government sites." As expected it happens hacktivist performs massive denial of service attacks multiple U.K. government websites over the country’s “draconian surveillance proposals” and “derogation of civil rights.” At the time of writing, the following websites are down: homeoffice.gov.uk (Home Office), number10.gov.uk (10 Downing Street - British Prime Minister’s Office), and justice.gov.uk (Ministry of Justice). A message on the site said the page was currently unavailable homeoffice.gov.uk "due to a high volume of traffic", suggesting a denial of service attack had been perpetrated. A message on Twitter claiming to be from Anonymous, a loosely organised group of hackers, said the action was "for your draconian surveillance proposals". The apparent attack came after it emerged last week that the Government was planning a massive expansion of its powers to monitor the email exchanges and website visits of every person in the UK. Under legislation expected in next month's Queen's Speech, internet companies will be instructed to install hardware enabling GCHQ - the Government's electronic "listening" agency - to examine "on demand" any phone call made, text message and email sent, and website accessed, in "real time" without a warrant.
A Home Office spokesman said: "We are aware of some reports that the Home Office website may be the subject of an online protest. We have put all potential measures in place and will be monitoring the situation very closely." The Home Office added that if a successful denial of service attempt did occur tonight, it would "liaise with the technical team and update as necessary".
A Home Office spokesman said: "We are aware of some reports that the Home Office website may be the subject of an online protest. We have put all potential measures in place and will be monitoring the situation very closely." The Home Office added that if a successful denial of service attempt did occur tonight, it would "liaise with the technical team and update as necessary".
-Source (The Huffington Post & BBC)