Posted by Avik Sarkar
On 12/05/2012 07:33:00 pm
'Dockster' A New Mac Malware Targeting Apple Users Found on Dalai Lama Related Website

Researcher at
F-Secure blog has identified that A new piece of malicious software targeted at
Apple users has been found on a
website dedicated to the
Dalai Lama. According to
blog post by F-Secure -the website related to
Dalai Lama is fully compromised and is pushing new Mac
malware, called
Dockster, using a
Java-based exploit. Dockster tries to infect computers by exploiting a vulnerability in Java,
CVE-2012-0507. The vulnerability is the same one used by the
Flashback malware, which first appeared around September 2011 and infected as many as
600,000 computers via a drive-by download. Flashback was used to fraudulently click on advertisements in order to generate illicit revenue in a type of scam known as click fraud. Apple patched the vulnerability in Java in early April and then undertook a series of steps to remove the frequently targeted application from Macs. Apple stopped bundling Java in the 10.7 version of its
Lion operation system, which continued with the company's Mountain Lion release. In October, Apple removed older Java browser plug-ins in a software update.
But still the matter of relief is that current versions of
OS X are not vulnerable; users who have disabled the Java browser plug-in are also not vulnerable. F-Secure researcher Sean Sullivan said Dockster is
“a basic backdoor with file download and keylogger capabilities.” Meanwhile F-Secure’s Sullivan, also said that the Dalai Lama’s site is also serving a Windows-based exploit for CVE-2012-4681, the Agent.AXMO Trojan. The Trojan exploits a Java vulnerability that allows remote code execution using a malicious applet that is capable of bypassing the Java SecurityManager.
While talking about Mac malware, then you must remember that earlier also Mac users faced such attacks when mac Trojan OSX.SabPub was spreading through Java exploits In 2011 we have also seen OSX/Revir-B trojan was installed behind a PDF, and giving hackers remote access to MAC computers, not only Revier-B also Linux Tsunami trojan Called "Kaiten"targeted Mac OS users in 2011. Also another malware named "Devil Robber" which was also make MAC users victim while stealing their personal information. In the very decent past we have seen a trojan named 'BackDoor.Wirenet.1' apparently providing its masters with a backdoor into infected systems. It is also capable of stealing passwords stored in browsers like Chrome, Chromium,Firefox and Opera. For any kind of cyber updates and infose news, stay tuned with VOGH.
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 9/23/2012 12:05:00 am
Social-Engineer Toolkit (SET) Version 4.0 Codenamed “Balls of Steel” Released
Social Engineer Toolkit also known as
SET gets another update. Now we have
Social Engineer Toolkit version 4.0 codename
“Balls of Steel” is officially available for public consumption. In his official blog; Trusted Sec, the developper of SET has claimed that this version of SET is
the most advanced toolkit till today. This version is the collection of several months of development and over
50 new features and
a number of enhancements, improvements, rewrites, and bug fixes.
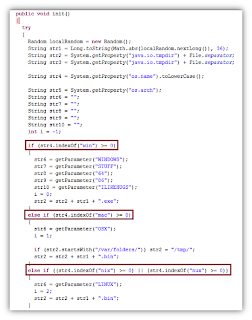
Lets talk about some highlights and the new major features of SET 4.0- the Java Applet attack has been completely rewritten and obfuscated with added evasion techniques. All of the payloads have been heavily encrypted with a number of heavy anti-debugging tools put in place. PyInjector is now available on the Java Applet attack natively and deploys shellcode automatically through a byte compiled executable. The powershell attack vectors now support customized payload selection through the config/set_config. A new attack vector has been added called the Dell DRAC Attack Vector (default credential finder). A new teensy payload has been added from the Offensive-Security crew – the auto-correcting attack vector with DIP switch and SDcard “Peensy”. The web cloner has been completely rewritten in native python removing the dependency for wget. The new IE zero day has been included in the Metasploit Web Attack Vector. The Java Repeater and Java Redirection has been rewritten to be more reliable. Obfuscation added to randomized droppers including OSX and Linux payloads.
Full Changelog of The Social-Engineer Toolkit (SET) 4.0:-
- Added a new attack vector to SET called the Dell Drac attack vector under the Fast-Track menu.
- Optimized the new attack vector into SET with standard core libraries
- Added the source code for pyinjector to the set payloads
- Added an optimized and obfuscated binary for pyinjector to the set payloads
- Restructured menu systems to support new pyinjector payload for Java Applet Attack
- Added new option to SET Java Applet – PyInjector – injects shellcode straight into memory through a byte compiled python executable. Does not require python to be installed on victim
- Added base64 encoded to the parameters passed in shellcodexec and pyInjector
- Added base64 decode routine in Java Applet using sun.misc.BASE64Decoder – native base64 decoding in Java is the suck
- Java Applet redirect has been fixed – was a bug in how dynamic config files were changed
- Fixed the UNC embed to work when the flag is set properly in the config file
- Fixed the Java Repeater which would not work even if toggled on within the config file
- Fixed an operand error when selecting high payloads, it would cause a non harmful error and an additional delay when selecting certain payloads in Java Applet
- Added anti-debugging protection to pyinjector
- Added anti-debugging protection to SET interactive shell
- Added anti-debugging protection to Shellcodeexec
- Added virtual entry points and virtualized PE files to pyinjector
- Added virtual entry points and virtualized PE files to SET interactive shell
- Added virtual entry points and virtualized PE files to Shellcodeexec
- Added better obfsucation per generation on SET interactive shell and pyinjector
- Redesigned Java Applet which adds heavily obfsucated methods for deploying
- Removed Java Applet source code from being public – since redesign of applet, there are techniques used to obfuscate each time that are dynamic, better shelf life for applet
- Added a new config option to allow you to select the payloads for the powershell injection attack. By specifying the config options allows you to customize what payload gets delivered via the powershell shellcode injection attack
- Added double base64 encoding to make it more fun and better obfuscation per generation
- Added update_config() each time SET is loaded, will ensure that all of the updates are always present and in place when launching the toolkit
- Rewrote large portions of the Java Applet to be dynamic in nature and place a number of non descriptive things into place
- Added better stability to the Java Applet attack, note that the delay between execution is a couple seconds based on the obfuscation techniques in place
- Completely obfsucated the MAC and Linux binaries and generate a random name each time for deployment
- Fixed a bug that would cause custom imported executables to not always import correctly
- Fixed a bug that would cause a number above 16 to throw an invalid options error
- Added better cleanup routines for when SET starts to remove old cached information and files
- Fixed a bug that caused issues when deploy binaries was turned to off, would cause iterative loop for powershell and crash IE
- Centralized more routines into set.options – this will be where all configuration options reside eventually
- Added better stability when the Java Applet Repeater is loaded, the page will load properly then execute the applet.
- The site cloner has been completely redesigned to use urllib2 instead of wget, long time coming
- The cloner file has been cleaned up from a code perspective and efficiency
- Added better request handling with the new urllib2 modules for the website cloning
- Added user agent string configuration within the SET config and the new urllib2 fetching method
- Added a pause when generating Teensy payloads
- Added the Offensive-Security “Peensy” multi-attack vector for the Teensy attacks
- Added the Microsoft Internet Explorer execCommand Use-After-Free Vulnerability from Metasploit into the Metasploit Browser Exploits Attack vectors
- Fixed a bug in cleanup_routine that would cause the metasploit browser exploits to not function properly
- Fixed a bug that caused the X10 sniffer and jammer to throw an exceptions if the folder already existed
To Download The Social-Engineer Toolkit (SET) 4.0 Click Here
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 9/20/2012 03:44:00 pm
Twitter Hires Renowned Apple Hacker Charlie Miller For Twitter Security Team
It is almost impossible task for
social networks to keep everything safe against hacks and other
vulnerabilities. Hackers will constantly find their way around anything that you put in place. So they often deals with hackers & turn themselves to beef up the security level. Social networking giant
Twitter exactly did the same thing. The micro-blogging network has hired the famous/infamous
Apple hacker,
Charlie Miller, to be a part of its security team.
Charlie Miller, a popular figure among hackers, broke the news via his
Twitter account, saying,
“Monday I start on the security team at Twitter. Looking forward to working with a great team there!” Twitter issued a short statement noting that Miller’s title will be that of Software Engineer, but declined to discuss any further details.
Charlie Miller has a background as a Global Exploitation Analyst in the National Security Agency, and has hacked devices running on
iOS,
OSX, and
Android. He is considered to be a
white-hat hacker, which means that he hacks to expose vulnerabilities in a system in order to have those weaknesses fixed. Five year ago, Miller was said to be the first to hack the
iPhone using the device’s browser, exposing the handset’s vulnerability to security attacks. Several months after this, he was likewise able to hack a
MacBook Air in just two minutes. This feat allowed Miller to win the
Pwn2Own hacking competition. Miller also showed a way to hijack iPhones through SMS in 2009. In 2011, he used the MacBook
power adapter to implant malware on the laptop. In the same year, his license as an Apple developer got revoked because Apple found that he breached the development agreement.
In more recent times, Miller had been working on Android devices. In June, he was able to overcome Bouncer,
Google’s security program. He has furthermore experience in using Near Field Communications to control Samsung and
Nokia handsets with a simple wave of another phone that is within the vicinity.
While talking about Charlie Miller, we must have to take another name and that is
Nicholas Allegra, the world-famous hacker known as
"Comex", creater of JailbreakMe.com; who later has been
hired by Apple itself . In case of Twitter we must have to say, apart from Miller, Twitter also hired
Moxie Marlinspike, a hacker who specializes in SSL and VPN encryption.
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 9/04/2012 03:34:00 pm
'BackDoor.Wirenet.1' Trojan Stealing Passwords From Mac & Linux Based Systems
A Russian Anti Virus software company named 'Dr Web' has spotted a piece of malware that unusually targeting Macs and Linux-based systems is causing a world of trouble for those in its path. The newly found mlaware dubbed 'BackDoor.Wirenet.1' apparently providing its masters with a backdoor into infected systems. It is also capable of stealing passwords stored in browsers like Chrome, Chromium, Firefox and Opera. Furthermore, it’s also able to obtain passwords from popular applications including SeaMonkey, Pidgin and Thunderbird. Even if you don’t use any of the above mentioned software, you’re still in danger as a keylogger is bundled in the payload. Wirenet.1 installs itself into the user's home directory using the name WIFIADAPT.
There are some steps that can be taken right away if you think you could be infected. Dr. Web is quick to point out that their anti-virus software will keep you protected. Another option is to simply disable communication with the control server used by the code’s author. In this case, blocking communication with IP address 212.7.208.65 should do the trick.
Earlier also Mac users faced such attacks when mac Trojan OSX.SabPub was spreading through Java exploits In 2011 we have also seen OSX/Revir-B trojan was installed behind a PDF, and giving hackers remote access to MAC computers, not only Revier-B also Linux Tsunami trojan Called "Kaiten"targeted Mac OS users in 2011. Also another malware named "Devil Robber" which was also make MAC users victim while stealing their personal information.
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 7/13/2012 01:53:00 am
Java-Based Multi-platform Backdoor Targeting Windows, Mac & Linux Computers
Security researcher at
Kaspersky Lab have revealed a new
java-based web vulnerability which is targeting Windows, Linux & Mac computers while installing backdoor. Mainly the whole thing is a Web-based social engineering attack that relies on malicious Java applets. According to security researchers from antivirus vendors
F-Secure - the attack was detected on a compromised website in Colombia. When users visit the site, they are prompted to run a Java applet that hasn't been signed by a trusted certificate authority.
If allowed to run, the applet checks which operating system is running on the user's computer -- Windows, Mac OS X or Linux -- and drops a malicious binary file for the corresponding platform.
The JAR file checks if the user's machine is running in Windows, Mac or Linux then downloads the appropriate files for the platform. All three files for the three different platforms behave the same way. They all connect to 186.87.69.249 to get additional code to execute. The ports are 8080, 8081, and 8082 for OSX, Linux, and Windows respectively.
The files are detected as:
Trojan-Downloader:Java/GetShell.A (sha1: 4a52bb43ff4ae19816e1b97453835da3565387b7)
Backdoor:OSX/GetShell.A (sha1: b05b11bc8520e73a9d62a3dc1d5854d3b4a52cef)
Backdoor:Linux/GetShell.A (sha1: 359a996b841bc02d339279d29112fe980637bf88)
Backdoor:W32/GetShell.A (sha1: 26fcc7d3106ab231ba0ed2cba34b7611dcf5fc0a)
However, since F-Secure researchers began monitoring the attack, the remote control server hasn't pushed any additional code. It appears that the attack uses the
Social Engineer Toolkit (SET), a publicly available tool designed for penetration testers, Aquino said Tuesday via email. However, the chances of this being a penetration test sanctioned by the website's owner are relatively low.
Kaspersky's researchers are in the process of analyzing the backdoor-type malware downloaded by the malicious shell code on Windows and Linux. "The Win32 backdoor is large, about 600KB; the Linux backdoor is over 1MB in size, both appear to contact very complex code which communicates encrypted with other servers."
-Source (CW & F-Secure)
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 5/05/2012 01:21:00 am
Microsoft Discovered a New Malware Targeting Apple OS X Exploiting Office Vulnerability
This year is going bad to worse for
MAC users. Earlier we have seen more than 600,000 Mac user infected by
Flashback Trojan after this one another Mac Trojan
"Backdoor.OSX.SabPub" penetrated mac security. Recently
Microsoft has detected a new piece of malware targeting Apple OS X computers that exploits a vulnerability in the Office productivity suite patched nearly three years ago. The malware is not widespread, according to Jeong Wook Oh of Microsoft's Malware Protection Center. But it does show that hackers pay attention if it's found people do not apply patches as those fixes are released, putting their computers at a higher risk of becoming infected.
The exploit discovered by Microsoft doesn't work with OS X Lion, but does work with
Snow Leopard and prior versions. Oh wrote that it is likely attackers have knowledge about the computers they are attacking, such as the victim's operating system version and patch levels. The malware delivered by the exploit is written specifically for OS X and is basically a "backdoor," or a tool that allows for remote control of a computer. Microsoft advised those who use Microsoft Office 2004 or 2008 for Mac or the Open XML File Format Converter for Mac to ensure those products have applied the patch.
-Source (Computer World)
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 4/22/2012 02:21:00 pm
Flashback Botnet Originated From Hacked & Malware-rigged WordPress Sites -Said Researchers
Massive Flashback botnet that hit more than 60K Mac PC world wide originated from hacked and malware-rigged WordPress blog sites. Researchers figure out there were between 30,000 and 100,000 WordPress sites infected in late February and early March, 85% of which are in the United States. Kaspersky Lab researchers say the infected WordPress blog sites were rigged with code that silently redirected visitors to a malicious server. "When the connection was made to the malicious server, that server would determine which OS was running and serve exploits accordingly," says Roel Schouwenberg, senior researcher for Kaspersky. It was a pay-per-install scheme to spread malware, including the Flashback Trojan.
Most researchers say a gradual decline in machines infected by the Trojan is still underway: As of Thursday, there were about 140,000 infected Macs still out there, according to Symantec, and Kaspersky says it sees only about 30,629 Flashback-infected bots in its sinkhole.
Still on the horizon, too, is the possibility of a Flashback comeback, with the command-and-control servers sending their bots updates. "We are watching the command-and-control domains used to control this botnet for any updates ... We haven't seen any new updates being delivered," said Liam O Murchu, manager of operations for Symantec Security Response. "Flashback generates new domains every day, which shows us the attackers have probably written malicious code before. They are aware that their botnet could be taken down with a single domain, so they generate a new one every day." To see the full story click here. Earlier also Mac users faced such attacks when mac Trojan OSX.SabPub was spreading through Java exploits In 2011 we have also seen OSX/Revir-B trojan was installed behind a PDF, and giving hackers remote access to MAC computers, not only Revier-B also Linux Tsunami trojan Called "Kaiten" targeted Mac OS users in 2011. Also another malware named "Devil Robber" which was also make MAC users victim while stealing their personal informations.
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 4/22/2012 02:21:00 pm
Apple Offering A Free DVD of Mac OSX Snow Leopard
You haven’t upgraded to Lion or iCloud because you still haven’t forked out money for Snow Leopard yet?If the answer is yes then we have a great news for you and that is
Apple is now giving away Snow Leopard to potential iCloud customers.
In an article sent to
MobileMe customers, Apple has recommended that potential customers get in touch with Apple to receive
a free DVD of Snow Leopard so that users can upgrade to Lion and move to iCloud. All you have to do is
follow this link, log in to MobileMe with your MobileMe account, and fill out your mailing information. Apple will then send you a Snow Leopard DVD for free. The free Snow Leopard offer was presumably initiated to encourage people to upgrade to
iCloud before MobileMe is shut down on June 30th, 2012.
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 4/20/2012 11:17:00 pm
Another Mac Trojan "Backdoor.OSX.SabPub" Discovered, Exploiting Java Vulnerability

Few weeks ago security experts found
Flashback Trojan infected more than 60,000
Mac users around the world. Immediately after this incident Apple issued
patches that curb the vulnerability. Yet again it has been found that another Mac trojan that is also spread through Java exploits. The malware, called
Backdoor.OSX.SabPub, can take screen-shots of a user’s current session, execute commands on an infected machine and connect to a remote website to transmit the data. It is not clear how users get infected with the trojan, but because of the low number of instances and the trojan’s backdoor functionality, Securelist speculates that it is most likely used in targeted attacks, possibly launched through emails containing a URL pointing to two one of websites hosting the exploit. Two versions of SabPub were discovered in the wild this past weekend, flying undedected for about two months now. Kaspersky's Costin Raiu wrote in a
blog post that SabPub was probably written by the
LuckyCat authors.
Version 1: Microsoft Office
One version of SabPub traps Mac (and potentially Windows) users with booby-trapped Microsoft Word documents which exploit the vulnerability 'MSWord.CVE-2009-00563.a.'
The spear-phishing emails containment a malicious Word attachment entitled '10thMarch Statemnet' (with typo) to Tibet sympathizers. March 10, 2011 refers to the day the Dalai Lama delivered his annual speech observing the Tibetan Uprising of 1959. The Word doc was created in August 2010 and updated in February with SabPub thrown in; "quite normal" for such attacks and seen in other APT's like Duqu, Raiu notes.
Version 2: Java
A March version of Sabpub also discovered last weekend exploits the same drive-by Java vulnerability seen in Flashback, one of the biggest botnet attacks seen in OS X. Once the backdoor Trojan is downloaded, a victim's system is connected to a command-and-control center via HTTP. From there the botnet can grab screenshots, upload/download files, and remotely execute commands, Sophos' Graham Cluley writes. SabPub drops the following two files on a user's system, so if you are concerned about infection Cluley recommends searching for these files:
/Users//Library/Preferences/com.apple.PubSabAgent.pfile
/Users//Library/LaunchAgents/com.apple.PubSabAGent.plist
Earlier also Mac users faced such attacks where
OSX/Revir-B trojan was installed behind a PDF, and giving hackers remote access to MAC computers, not only Revier-B also
Linux Tsunami trojan Called "Kaiten" targeted Mac OS users in 2011. Also another malware named
"Devil Robber" which was also make MAC users victim while stealing their personal informations.
-Source (Securelist & PC Mag)
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 2/26/2012 10:44:00 pm
Flashback.G Trojan Targeting Mac Users While Stealing Passwords
Remember earlier MAC Security Blog reported that the latest version,
Flashback.D, has gotten a bit sneakier. First, it checks to see if the user is running Mac OS X in VMware Fusion. If so, it does not execute. It does this because many malware researchers test malware in virtual machines, rather than infect full installations, as it is easier to delete them and start over with clean copies. This means that security researchers analyzing and looking for this malware need to be running regular Macs.
Yet again Mac users became the victim of another trojan. This new Trojan virus is capable of infecting their computers and stealing passwords to services such as Google, PayPal, online banking & so on. This virus is using a new installation method When a user visits a crafted web page, the new variant either tries to exploit two old security vulnerabilities or deploys a Java Applet which tries to trick the user into believing it has been certified by Apple. According to
Mac Security Blog (Intego):- This new variant of the Flashback Trojan horse uses three methods to infect Macs. The malware first tries to install itself using one of two Java vulnerabilities. If this is successful, users will be infected with no intervention. If these vulnerabilities are not available – if the Macs have Java up to date – then it attempts a third method of installation, trying to fool users through a social engineering trick. The applet displays a self-signed certificate, claiming to be issued by Apple. Most users won’t understand what this means, and click on Continue to allow the installation to continue.
It is worth noting that
Flashback.G will not install if VirusBarrier X6 is present, or if a number of other security programs are installed on the Mac in question. It does this to avoid detection. It seems that the malware writers feel it is best to avoid Macs where the malware might be detected, and focus on the many that aren’t protected.
Earlier also Mac users faced such attacks where
OSX/Revir-B trojan was installed behind a PDF, and giving hackers remote access to MAC computers, not only Revier-B also
Linux Tsunami trojan Called "Kaiten" targeted Mac OS users in 2011. Also another malware named
"Devil Robber" which was also make MAC users victim while stealing their personal informations.
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 2/14/2012 12:29:00 am
THC-HYDRA Updated Version 7.2 Released
Earlier we have discussed many times about
THC-HYDRA. Now the developer officially released the updated version of the world's one of the most fastest login cracker Ver 7.2. This tool is a proof of concept code, to give researchers and security consultants the possibility to show how easy it would be to gain unauthorized access from remote to a system. It was tested to compile cleanly on Linux, Windows/Cygwin, Solaris, FreeBSD and OSX. Additional information can be found
here
Official Change Log:-
- Speed-up http modules auth mechanism detection
- Fixed -C colonfile mode when empty login/passwords were used (thanks to will(at)configitnow(dot)com for reporting)
- The -f switch was not working for postgres, afp, socks5, firebird and ncp, thanks to Richard Whitcroft for reporting!
- Fixed NTLM auth in http-proxy/http-proxy-url module
- Fixed URL when being redirected in http-form module, thanks to gash(at)chaostreff(dot)at
- Fix MSSQL success login condition, thanks to whistle_master(at)live(dot)com
- Fix http form module: optional headers and 3xx status redirect, thx to Gash
- Fix in configure script for –prefix option, thanks to dazzlepod
- Update of the dpl4hydra script by Roland Kessler, thanks!
- Small fix for hydra man page, thanks to brad(at)comstyle(dot)com
To Download THC-HYDRA 7.2 Click Here
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 1/15/2012 12:12:00 am
Hello BSD user I have 2 good news for you and that is both Free BSD & PC BSD 9 has been released.
Brief About FreeBSD:-
FreeBSD is an advanced operating system for modern server, desktop, and embedded computer platforms. FreeBSD's code base has undergone over thirty years of continuous development, improvement, and optimization. It is developed and maintained by a large team of individuals. FreeBSD provides advanced networking, impressive security features, and world class performance and is used by some of the world's busiest web sites and most pervasive embedded networking and storage devices. For more information about this release click
here.
Some Highlights:-
- The FreeBSD Release Engineering Team is pleased to announce the availability of FreeBSD 9.0-RELEASE. This is the first release from the stable/9 branch, which improves on stable/8 and adds many new features.
- A new installer, bsdinstall(8) has been added and is the installer used by the ISO images provided as part of this release
- The Fast Filesystem now supports softupdates journaling
- ZFS updated to version 28
- Updated ATA/SATA drivers support AHCI, moved into updated CAM framework
- Highly Available Storage (HAST) framework
- Kernel support for Capsicum Capability Mode, an experimental set of features for sandboxing support
- User-level DTrace
- The TCP/IP stack now supports pluggable congestion control framework and five congestion control algorithm implementations available
- NFS subsystem updated, new implementation supports NFSv4 in addition to NFSv3 and NFSv2
- High Performance SSH (HPN-SSH)
- Flattened device tree (FDT), simplifying FreeBSD configuration for embedded platforms
- The powerpc architecture now supports Sony Playstation 3
- The LLVM compiler infrastructure and clang have been imported
- Gnome version 2.32.1, KDE version 4.7.3
To Download FreeBSD 9 Click Here ******
Brief About PC-BSD:-
PC-BSD is a user friendly desktop Operating System based on FreeBSD. Known widely for its stability and security in server environments, FreeBSD provides an excellent base on which to build a desktop operating system. PC-BSD uses a host of popular open source window managers and uses a custom-tailored application installer that puts popular applications in easy reach of users. For more information click Here
Some Highlights:-
- Based upon FreeBSD 9.0-RELEASE
- Support for installing a variety of Window Managers, such as KDE, GNOME, XFCE, LXDE and more!
- Improved PBI system, allows library sharing, binary diff updating, custom repositories, digital signing and more!
- Support for "freebsd-update" via the System Update GUI.
- New Control Panel, providing consistent configuration options across various Window Managers.
- Improved networking utilities, including wifi quick-connect.
- Enhanced "Life-Preserver" utility for doing off-site rsync backups of user data.
- New VirtualBox / VMware disk images, with integrated guest tools.
- Support for UFS+Journaling out of box
- New graphical boot options page
- Support for installation to BootCamp partitions on OSX systems.
- And much more!
To Download PC-BSD 9 Click Here *****
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 12/28/2011 04:48:00 pm
TeamViewer 7 for Windows was released about a month ago now the Ver 7 is available for Linux though its a beta release. TeamViewer is an application for remote control, desktop sharing and file transfer between computers, great for meetings, presentations, support and more. It runs on Windows, Mac OSX, Linux (even though it comes in a .deb or .rpm, it uses Wine which comes bundled with it) as well as Android or iPhone. The application is free for personal use only.
What is New In TeamViewer 7 :-
- Enhanced multi-monitor support
- An integrated screenshot tool
- Record presentations
- Save connection settings per Computer (store individual connection settings for each computer in your Computers & Contacts list) - see the first screenshot in the post
- Instant meeting (you can start your meeting even before adding any participants - ideal for preparation and testing)
- Scheduled meetings
- Mobile participation via Android / iOS client
- File Box (make files available for download during meeting)
To Download TeamViewer 7 Click Here
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 11/02/2011 05:03:00 pm
"DevilRobber" Trojan Infects Mac OS-X & Stealing Personal Information (Credit Cards, User-name, Passwords & so on).
Now another piece of malware has struck unsuspecting Mac owners. The new multiplatform trojan is much more sophisticated than most of the past malware to hit the Mac platform. The malicious program installs as part of infected torrent downloads from sites such as The Pirate Bay. Thus far the malware has been primarily found to be piggybacking on pirated copies of the image editing app GraphicConverter version 7.4 (whose authors are not involved in the screen and do not approve of the pirating in the first place). The onboard malware is officially known in security circles as OSX/Miner-D, and is nicknamed the "DevilRobber".
Once installed on the victim's machine, the malware opens a back-door to the OS X system, allow remote command-and-control. It also monitors your computer, attempting to
steal personal information like credit cards.
To do this it takes screenshots. It also periodically dumps confidential information from various applications -- such as truecrypt data, Vidalia (TOR plugin for Firefox), your Safari browsing history, and .bash_history -- into the creatively named file dump.txt. It also records your username and passwords via monitoring using a proxy server (on port 34522 in the most common variant, but likely to change).
-News Source (NS, Intego, Dailytech)
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 9/29/2011 07:07:00 pm
Apple has updated the bare-bones antivirus protection included with Mac OS X to detect a Trojan horse that poses as a PDF document. That Trojan, named
"Revir.A" by Finnish security company F-Secure but "Revir.B" by others, masquerades as a PDF file . Unwary users who download and open the fake PDF actually start a malware chain reaction that infects a Mac with multiple pieces of attack code, including a
"backdoor" designed to listen to a hacker-controlled server for further instructions.
Apple added a signature for Revir on Friday to the detection engine called XProtect included with Mac OS X 10.6, aka Snow Leopard, and Mac OS X 10.7, better known as Lion. Since May, when Apple fought a weeks-long battle with makers of phony Mac security software -- usually called "scareware" or "rogueware" -- XProtect checks daily for new signature updates.
The new signature will detect Revir if a user downloads the fake PDF document using Safari, iChat or Mail -- Mac OS X's native email client -- and then displays a warning urging the user to toss the file into the Trash. On Monday, however, Mac-centric security company Intego said it had spotted a new piece of Mac malware disguised as an Adobe Flash installer.
Tagged "Flashback" by Intego, the Trojan installs itself when the fake Flash file is run, then deactivates the Mac outbound firewall Little Snitch , likely as an attempt to hide communication between the malware and its remote command-and-control server.
Flashback uses the same phony Flash distribution tactic as a Trojan horse named "QHost.WB" found by F-Secure in early August. Apple updated XProtect to detect QHost on Aug. Intego speculated that hackers may think the Flash installer trick will be effective because Lion, unlike earlier Mac OS X editions, does not come with the Adobe software pre-installed.
The French antivirus firm recommended that users download Flash Player only from Adobe's website, and if they're using Safari, to uncheck the box marked "Open 'safe' files after downloading" under the General tab to prevent fake installers like Flashback from running automatically.
-News Source (Network World)
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 9/25/2011 02:02:00 am

A fascinating new example of Mac malware has been discovered, that appears to be adopting an old Windows-style disguise to fool users into running it. Despite the numerous times that cybercriminals have created boobytrapped PDF files that exploit vulnerabilities to infect unsuspecting users, many people still think that PDF files are somehow magically safer to open than conventional programs.The OSX/Revir-B Trojan plays on this by posing as a PDF file.
When the malicious Macintosh application file is run it tries to drop a PDF embedded inside it onto the user's hard drive. The Chinese language PDF file displayed is about a controversial topic, "Do the Diaoyu Islands belong to Japan?" The Diaoyu Islands (known as the Senkaku islands in Japan) are the subject of a long-running dispute between the two countries, with both claiming sovereignty. The malware attempts to install a backdoor Trojan horse (detected by Sophos as OSX/Imuler-A) which would give malicious hackers remote access to your Apple Mac computer.
TO download the Patch Click
Here
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 9/16/2011 02:16:00 pm
THC-HYDRA is a very fast network logon cracker which support many different services. This tool is a proof of concept code, to give researchers and security consultants the possibility to show how easy it would be to gain unauthorized access from remote to a system. It was tested to compile cleanly on Linux, Windows/Cygwin, Solaris, FreeBSD and OSX.
Official change log for THC-HYDRA v7.0:-
- New main engine for hydra: better performance, flexibility and stability
- New option -u – loop around users, not passwords
- Option -e now also works with -x and -C
- Added RDP module, domain can be passed as argument
- Added other_domain option to smb module to test trusted domains
- Small enhancement for http and http-proxy module for standard ignoring servers
- Lots of bugfixes, especially with many tasks, multiple targets and restore file
- Fixes for a few http-form issues
- Fix smb module NTLM hash use
- Fixed Firebird module deprecated API call
- Fixed for dpl4hydra to work on old sed implementations (OS/X …)
- Fixed makefile to install dpl4hydra (thx @sitecrea)
- Fixed local buffer overflow in debug output function (required -d to be used)
- Fixed xhydra running warnings and correct quit action event
To download THC-HYDRA ver7.0 Click
Here
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 7/15/2011 05:25:00 pm
THC-HYDRA is a very fast network logon cracker which support many different services. This tool is a proof of concept code, to give researchers and security consultants the possibility to show how easy it would be to gain unauthorized access from remote to a system. It was tested to compile cleanly on Linux, Windows/Cygwin, Solaris, FreeBSD and OSX
New Features of THC Hydra v6.5:-- Added dpl4hydra script by Roland Kessler, which creates a default password for a device. Thanks!
- Improved HTTP form module: getting cookie, fail or success condition, follow multiple redirections, support cookie gathering URL, multiple user defined headers
- Added interface support for IPv6, needed for connecting to link local fe80:: addresses. Works only on Linux and OS/X. Information for Solaris and *BSD welcome
- Added -W waittime between connects option
- The -x bruteforce mode now allows for generated password amounts > 2 billion
- Fix if -L was used together with -x
- Fixes for http- modules when the http-…://target/options format was used
- Fixed a bug in the restore file write function that could lead to a crash
- Fixed XMPP module jabber init request and challenge response check, thx “F e L o R e T”
- Fix: if a proxy was used, unresolveable targets were disabled. now its fine
- Fix for service://host/ usage if a colon was used after the URI without a port defined
Download THC-HYDRA v6.5 (hydra-6.5-src.tar.gz) here.
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 6/18/2011 01:13:00 am
One of the most famous network logon cracker – THC-HYDRA, has been updated. We now have THC-HYDRA version 6.4!
THC-HYDRA is a very fast network logon cracker which support many different services. This tool is a proof of concept code, to give researchers and securityconsultants the possibility to show how easy it would be to gain unauthorized access from remote to a system. It was tested to compile cleanly on Linux,Windows/Cygwin, Solaris, FreeBSD and OSX.
Changelog for thc-hydra v6.4
Update SIP module to extract and use external IP addr return from server error to bypass NAT
Update SIP module to use SASL lib
Update email modules to check clear mode when TLS mode failed
Update Oracle Listener module to work with Oracle DB 9.2
Update LDAP module to support Windows 2008 active directory simple auth
Fix to the connection adaptation engine which would loose planned attempts
Fix make script for CentOS, reported by ya0wei
Print error when a service limits connections and few pairs have to be tested
Improved Mysql module to only init/close when needed
Added patch from the FreeBSD maintainers
Module usage help does not need a target to be specified anymore
configure script now honors /etc/ld.so.conf.d/ directory
Download THC-HYDRA v6.4 (hydra-6.4-src.tar.gz) here.
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-
Posted by Avik Sarkar
On 5/19/2011 10:38:00 pm
 Malware Threats for Apple Inc.’s Macintosh operating system are getting worse, and Apple’s official policy is not to help get rid of the problem.
Malware Threats for Apple Inc.’s Macintosh operating system are getting worse, and Apple’s official policy is not to help get rid of the problem.
These were the admissions of an AppleCare call center representative who spoke to tech website ZDNet’s Ed Bott, who posted the transcript of the conversation on ZDNet’s site.
“We started getting a trickle of calls a couple weeks ago. However, this last week over 50 percent of our calls have been about it. In two days last week I personally took 60 calls that referred to Mac Defender," said the representative.
Mac Defender is a rogue software masquerading as an anti-malware program for computers running the Mac OSX operating system.
It presents bogus messages and charges users to pay for the program.
'We're not supposed to help customers:-
But the representative said that they had been advised to adopt a passive stance against Mac Defender and any other such malware. “we’re not supposed to help customers remove malware from their computer," the representative said.
“The reason for the rule, they say, is that even though Mac Defender is easy to remove, we can’t set the expectation to customers that we will be able to remove all malware in the future. That’s what antivirus is for," the representative said.
But the representative admitted some call center representatives still try to help, despite an agreement for AppleCare that they are not supposed to help with malware.
“Indeed we are monitored, but I can’t personally justify telling a father who’s freaking out about what his 6-year-old daughter just saw that I can’t help him out. Our on-floor managers and QA guys do their best to let it slide, but if they start getting pushed from higher-ups, we could face write-ups and even termination," the representative said.
'It's getting worse':-
The representative also said the problem with Mac Defender is getting worse.
“It started with one call a day two weeks ago, now it’s every other call. It’s getting worse. And quick," the rep said.
The rep added they would also give callers whose computers were hit links to antivirus software makers.
SHARE OUR NEWS DIRECTLY ON SOCIAL NETWORKS:-












+Version+4.0.jpg)